SERVICES
Most small and mid-sized organizations know they need better security — they just don’t know where to start, who to trust, or how to make sense of it all. Maltek Solutions exists to change that. We make cybersecurity approachable, collaborative, and actually useful for organizations without a dedicated security team.
TESTING & ASSESSMENT
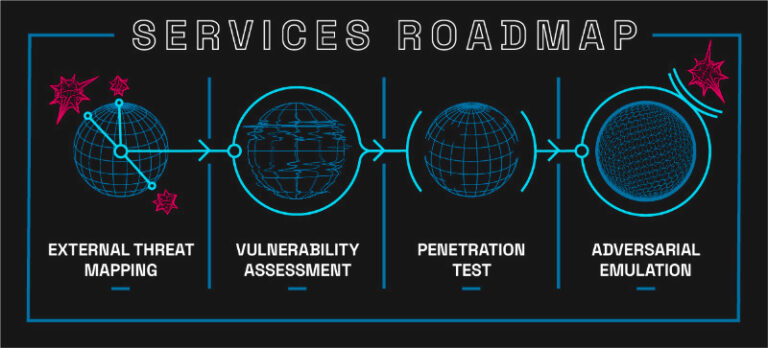
>> Start your security journey with a comprehensive assessment that gives you a clear, honest picture of where you stand.
Our Security Assessment services are the foundation of a strong security posture. Whether you’re starting from scratch or validating existing controls, we work with your team from start to finish — collaborating on scope, executing thorough testing, and delivering clear, prioritized findings you can actually act on.
We don’t hand you a massive stack of raw scan data. We validate every finding, filter out the noise, and give you a report that explains the risk in plain language — because understanding your vulnerabilities is just as important as finding them.
EXTERNAL THREAT MAPPING
Many organizations don’t have an accurate picture of how they appear to the outside world. External Threat Mapping, also known as attack surface mapping, identifies every externally facing asset, service, and entry point that a threat actor could target. We map your full external footprint so you know exactly what you’re defending.
VULNERABILITY ASSESSMENTS
Our rapid-delivery vulnerability assessments are an excellent entry point for organizations beginning their security journey. Assessments can be performed across internal networks, external networks, and web applications. We combine industry-standard tooling with our own proprietary filtering process to deliver prioritized, easy-to-understand results.
>> Take the next step on the road to a secure infrastructure.
PENETRATION TESTING
Maltek penetration tests go beyond automated scanning. We simulate real-world attackers to find the vulnerabilities that matter most to your business. We collaborate with your team at every stage: scoping the engagement, executing the test, and walking through findings with clear impact assessments and remediation guidance.
Our penetration testing services cover:
External Penetration Testing
External tests focus on the means of entry into your internal network. All of your public-facing hosts, network services you provide, and public-facing network infrastructure are evaluated. Any potential means of entry is identified and assigned risk criteria.
Internal Penetration Testing
Internal tests focus on post-foothold activity. We simulate an attacker’s ability to exploit vulnerabilities, escalate privileges, and move laterally throughout the network.
Web Application Testing
Web application tests utilize an OWASP-aligned methodology to comprehensively test your critical web applications for vulnerabilities that may be exploited to damage your business
Cloud Security Review
Don’t leave your business’ security solely in the hands of your cloud providers! Our cloud testing incorporates a review of Identity and Access Management (IAM) profiles, storage accounts, network security, logging and monitoring, and key management services that are critical to ensuring no unauthorized access results from your cloud infrastructure.
Wireless Network Testing
Wireless tests evaluate your wireless networks by performing a comprehensive review that aligns with industry-leading practices.
CUSTOM SOLUTIONS
We do it all. Our in-house solutions and network of resources cover every domain of security infrastructure. Tell us what you need, and we will tailor a custom solution to fit your needs at a fraction of the cost you’ll see from other providers.
ADVISORY & STRATEGY
>> Your cybersecurity program should be built around your business — not a one-size-fits-all checklist.
Our Advisory & Strategy services are designed for organizations that need more than a one-time test. We serve as a trusted extension of your team — helping you build a security program that’s aligned with your business objectives, your risk tolerance, and the realities of your budget and staffing.
This is where we help you move from reactive to strategic. We translate complex security concepts into clear decisions, work alongside your existing IT staff and vendors, and provide the expert guidance that helps leadership feel confident about where the organization stands.
RISK ASSESSMENT & FRAMEWORK DEVELOPMENT
We help organizations identify, analyze, and prioritize their security risks using structured, data-driven methodologies. Our team builds custom security frameworks aligned with industry standards, including NIST CSF, ISO 27001, CIS Controls, and HITRUST. tailored specifically to your environment, not pulled from a generic template.
- Security risk framework development aligned to NIST, ISO 27001, CIS, or HITRUST
- Threat modeling to identify attack vectors unique to your business
- Risk quantification: measuring impact and likelihood to prioritize what to fix first
- Compliance gap analysis against HIPAA, PCI-DSS, SOC 2, GDPR, and other frameworks
- Third-party and vendor risk assessment
STRATEGIC SECURITY PLANNING
Great security doesn’t happen by accident — it’s the result of deliberate planning. We work with your leadership team to develop a security roadmap that balances risk reduction with operational and financial realities. You’ll walk away with a prioritized plan you can actually execute, along with the metrics and reporting mechanisms to track your progress over time.
- Multi-year security roadmap development
- Security policy, procedure, and controls documentation
- Incident response planning and tabletop exercise facilitation
- Monitoring and reporting frameworks for ongoing visibility
- Board and leadership-level security briefings
VIRTUAL CISO (vCISO)
Not every organization needs — or can afford — a full-time Chief Information Security Officer. Our Virtual CISO service gives you senior-level cybersecurity leadership on a flexible, ongoing basis. We integrate with your team to provide strategic oversight, help you navigate complex decisions, and ensure your security program matures alongside your business.
The vCISO relationship is built around your needs, whether that’s monthly advisory sessions, support through a compliance audit, or hands-on guidance during a security incident. We serve as the cybersecurity expert your team can turn to without the overhead of a full-time executive hire.
- Ongoing strategic cybersecurity leadership and oversight
- Security program development and maturity assessment
- Executive and board-level communication and reporting
- Vendor and MSP security coordination
- Regulatory compliance navigation (HIPAA, PCI-DSS, SOC 2, NERC CIP, and others)
- Incident response leadership and post-incident review
COMPLIANCE & REGULATORY GUIDANCE
Navigating regulatory requirements is complex — and the consequences of getting it wrong are significant. We help you understand what compliance actually requires, assess where you currently stand, and build a path to meeting your obligations without creating unnecessary operational friction
- HIPAA, PCI-DSS, SOC 2, GDPR compliance gap analysis and remediation planning
- NIST CSF and CIS Controls alignment
- Cyber insurance readiness assessment
- Support for electric cooperative cybersecurity goals and frameworks
TRAINING & EDUCATION
>> In 2022, 98% of attacks included a social engineering component. Your people are your most important security control.
Technical defenses only go so far. The most sophisticated firewall in the world won’t stop an employee who clicks a malicious link or hands over credentials over the phone. Our Training & Education services turn your workforce from a vulnerability into a frontline of defense.
We don’t deliver generic slide decks. We connect with your team in plain language, clearly explaining how attacks work, how to recognize them, and exactly what to do when something looks suspicious. Our training is practical, engaging, and built around the threats your organization actually faces.
SECURITY AWARENESS TRAINING
Our security awareness training programs are designed for real people, not security professionals. We cover the most common attack vectors — phishing, vishing, pretexting, and more — and give your team the confidence to recognize and respond appropriately. Training can be delivered across all levels of the organization, with role-specific content where needed.
- Organization-wide security awareness training
- Role-based training tailored to different departments and risk levels
- Clear, jargon-free content that resonates with non-technical staff
- Progress tracking and improvement measurement over time
CUSTOM SOCIAL ENGINEERING CAMPAIGNS
Knowing your team has been trained is one thing — knowing how they actually perform under pressure is another. Our custom social engineering campaigns put your training to the test with realistic, tailored simulations that reveal where gaps still exist.
We design and execute campaigns that simulate real-world attacker behavior — phishing emails, phone-based pretexting, physical security tests — and deliver clear results that show you where your people excel and where additional focus is needed. Each campaign is followed by a debrief that reinforces the learning rather than creating fear or blame.
- Custom phishing email campaigns
- Vishing (phone-based social engineering) simulations
- Physical security and tailgating assessments
- Campaign results reporting with actionable next steps
- Post-campaign training reinforcement
Start taking measures to protect your assets.
